Key messages:
- The development of decision-relevant climate change risk assessment with a holistic approach requires an exploratory, iterative and adaptive process that will take time. A holistic approach
considers physical, transition and litigation risks and their interactions at different time horizons in the short and long term. It considers both sides of the balance sheet, as well as interactions across business functions and decision feedback loops to assess the materiality of risks and develop potential actions to address them. Importantly, some re/insurers that have advanced further in this iterative process have found it beneficial to anchor the assessment in overarching decision areas that link both sides of the balance sheet. While re/insurers in all business lines have started exploring the materiality of physical and transition climate change risks on each side of the balance sheet, for life & health re/insurers in particular, more research is required to assess the attributions and materiality of climate change to their underwriting exposures – including longevity, mortality and morbidity –over various time horizons. As research in this field progresses, the ability both to assess life & health re/insurer liability exposures and perform more holistic assessments will improve. - An analysis of regulatory developments since June 2021 and a survey conducted by The Geneva Association reveal that the regulatory and supervisory priorities and approaches are increasingly aligned with earlier GA task force recommendations related to climate change risk assessment and scenario analysis.
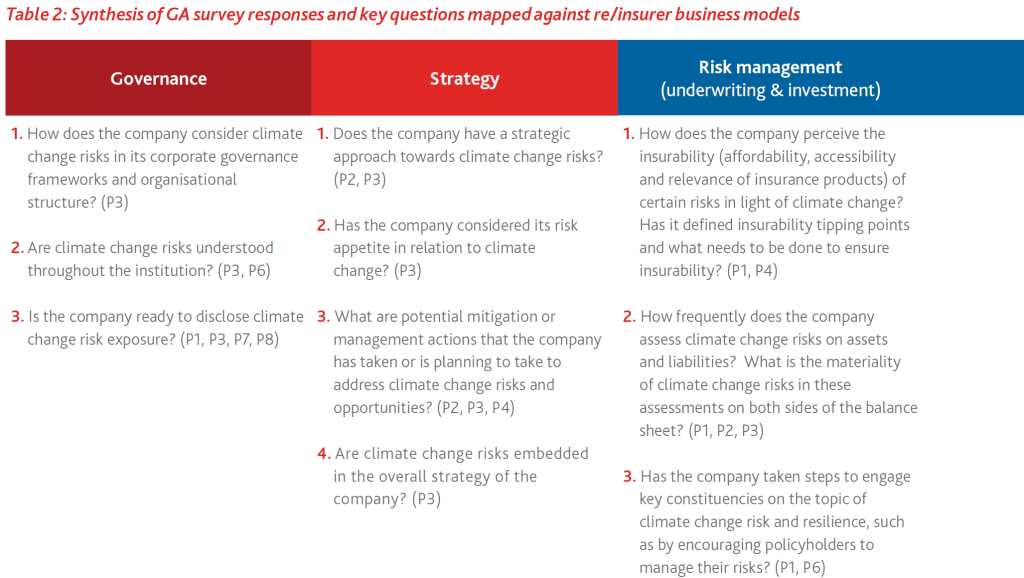
- Responses from 11 regulatory bodies to a Geneva Association Survey shed light on the regulatory objectives and priorities that can help guide climate change risk assessment exercises within and across jurisdictions. Our analysis has revealed the top four regulatory priorities:
- policyholder protection,
- the insurer’s financial health,
- corporate governance and strategy,
- the insurability/affordability of insurance solutions,
- financial stability,
- raising risk awareness,
- addressing data/risk assessment services and environmental stewardship.
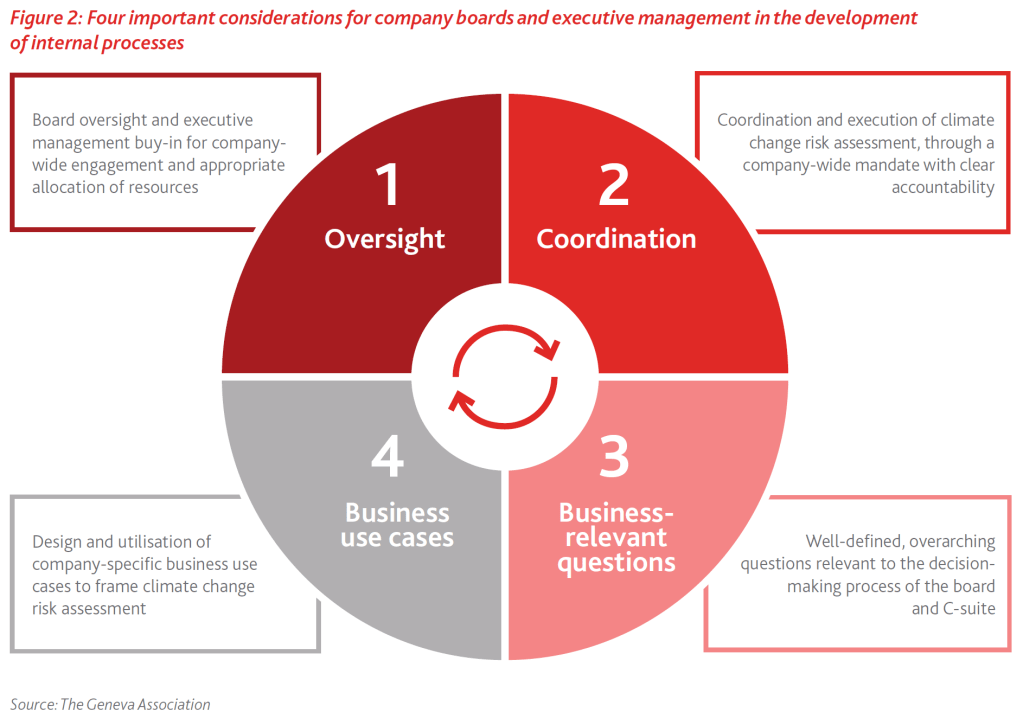
- Company boards and executive management need to consider the following four key issues to drive the process towards a more holistic approach that would produce decision-useful information:
- Board oversight and executive management buy-in for company-wide engagement, along with appropriate resource allocation to build these capabilities, are important;
- The coordination and execution of climate change risk assessment require an internally established, company-specific mandate with clear accountability;
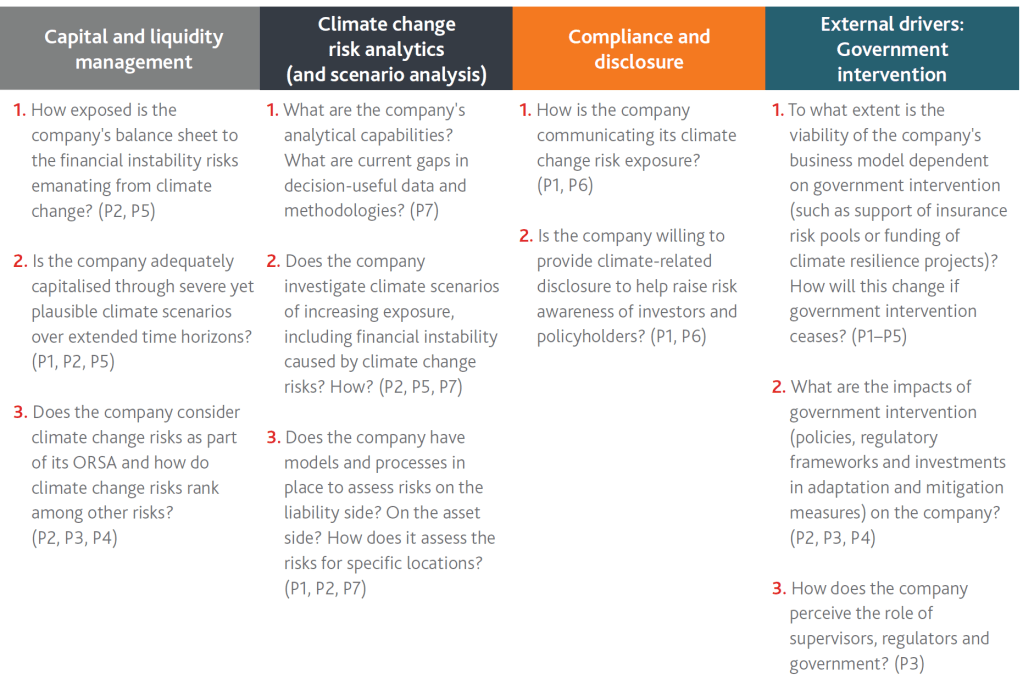
- Central to this process is the development of overarching decision-relevant questions for the board and the C-suite (a list based on the GA survey of regulatory and standard-setting bodies is included);
- Company-relevant business use cases should be designed and utilised to guide the iterations of climate change risk assessment.
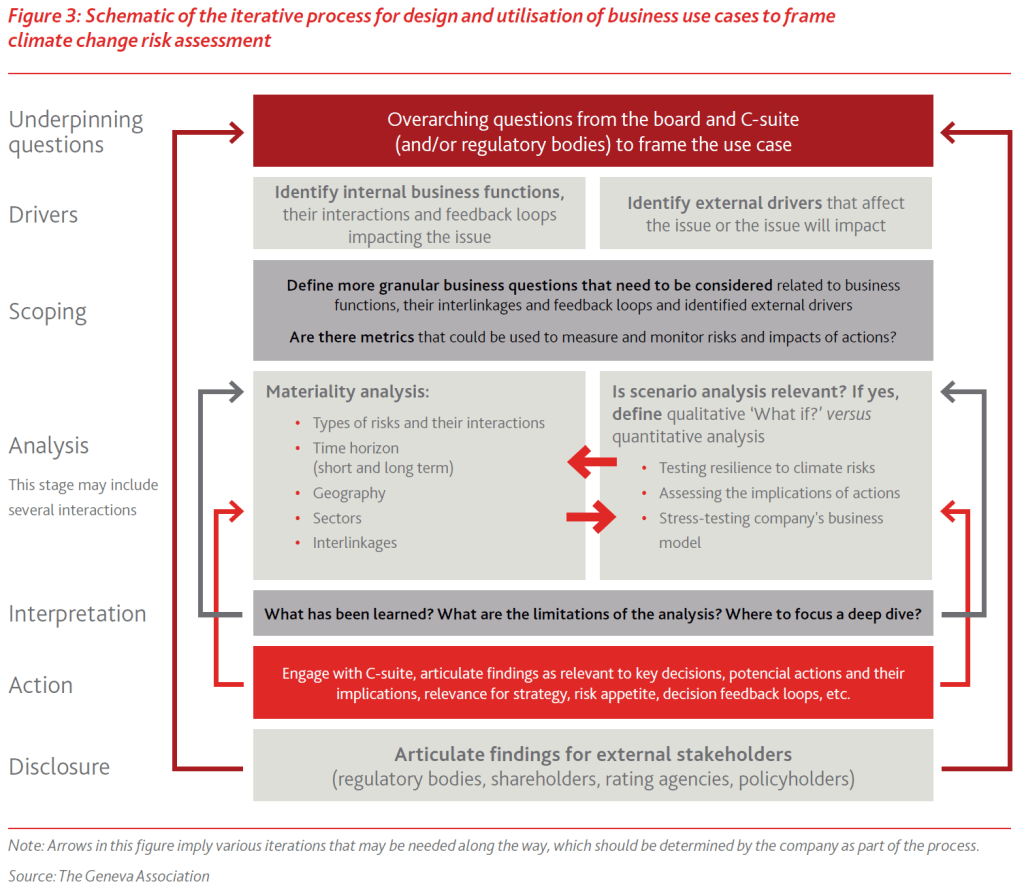
- A 10-step template provided in this report can help companies design business use cases to frame the analysis, engage experts from relevant business functions across the balance sheet, and mine and utilise the same data and tools across the company. It is important to start simple by exploring the impacts of each climate change risk type, on each side of the balance sheet, considering short- and long-term time horizons. With each iteration, companies can build up the level of complexity by assessing the interactions of physical, transition and litigation risks and exploring how these risks are manifested within and across business functions. Of note:
- This process should consider internal business functions and their interactions as well as external drivers that impact issues relevant to the business use case, by risk type and time horizon;
- Materiality analysis is at the heart of climate change risk assessment, allowing focus on the
areas most impacted by climate change risks and identifying priorities for a deeper dive and
resource allocation; - As part of the design and implementation of business use cases, the company should seek to
identify metrics to measure and monitor the risks and track the impacts of the measures taken to manage them; - This resource-intensive process will take time and present challenges that will need to be addressed, ranging from overtime and the availability of data for the given region to internal experience and expertise, and the availability of best practices. In this report, we offer three examples of business use cases to demonstrate these points.
- The use of forward-looking scenario analysis needs to be further explored, depending on the issue being considered. Scenario analysis is a tool for conducting a forward-looking assessment of risks and opportunities, where the company can systematically explore individual or combined factors and make strategic decisions in the face of significant uncertainties. Scenario analysis may be used for a range of applications, for example:
- Testing the resilience of a company’s business model to climate change-related risks;
- Assessing the implications of possible actions a company can take;
- Stress-testing the company’s business model under extremely adverse conditions.
- Through strong industry collaboration, re/insurers should conduct an analysis of existing data challenges, gaps and needs, and define priority areas and requirements for the future development of tools. More work is required by re/insurers and regulatory bodies to identify gaps in data, to converge on best practices and build a robust toolbox for forward-looking climate change risk analyses. Since 2021, several organisations have offered an assessment of the gaps in climate change risk data and tools in the current landscape, with a focus on certain applications or segments in the financial sector. The journey towards a holistic approach could lead re/insurers to address such gaps over time, not least in emissions data, asset locations and supply chain data. Note that life & health re/insurers still face challenges when it comes to identifying the types of data that would allow the extraction of climate change attribution and liability exposures.
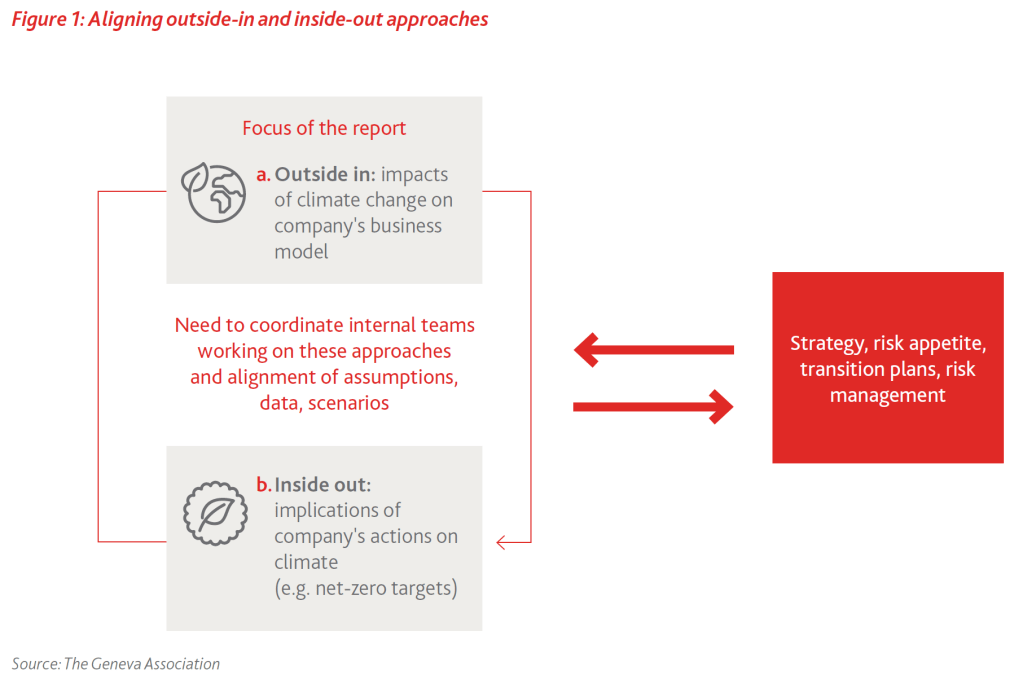
- Importantly, company leadership should seek to harmonise and align their net-zero target-setting
activities using ‘inside-out’ analysis with efforts to assess the resilience of their business model to
climate change risks using ’outside-in’ approaches for developing viable targets, transition strategy and plans. In fact, a growing number of critics are calling out the misalignment of net-zero pledges with what the companies can actually deliver and the possibility of greenwashing, which could lead to potential reputational and climate litigation risks or even regulatory action. - Robust intra- and inter-sectoral collaboration is the only way to expedite the development and convergence of good practices, meaningful baseline requirements for decision-useful climate change risk assessments and disclosures that would allow for cross-company comparisons. To this end, we acknowledge and deeply appreciate the growing proactive collaboration and engagement
across the insurance industry and with key regulatory and standard-setting bodies in the financial sector.
Context
In 2020, The Geneva Association (GA) launched its task force on climate change risk assessment with the aim of advancing and accelerating the development of holistic methodologies and tools for conducting forward-looking climate change risk assessment. These efforts have intended not only to support primary insurance and reinsurance companies and regulatory bodies with innovation in this area, but also to demonstrate the benefits of industry-level collaboration to help expedite the development and convergence of best practices.
In its first two reports, the GA task force highlighted the complexities associated with the development of forward-looking climate change risk assessment methodologies and tools. It stressed the need to develop methodologies for holistic climate change risk modelling and scenario analysis for both sides of the balance sheet, using a combination of qualitative and quantitative approaches. The GA task force also highlighted the implications of physical and transition risks for the insurance industry, with a focus on the challenges of quantitative scenario analysis approaches. The conclusion was that the prescriptive quantitative regulatory exercises to date, which were conducted to raise awareness, have outlived their
purpose. More specifically, these resource-intensive exercises do not provide decision-useful information given the significant uncertainties associated with the transition to a carbon-neutral economy (e.g. uncertainties associated with public policy, market and technology risks). Finally, the GA task force called on regulatory bodies to clarify their regulatory objectives and explain how their exercises would deliver decision-useful information. It also stressed the need for convergence on baseline regulatory requirements for analysis and reporting across jurisdictions. To this end, it encouraged stronger collaboration between regulatory bodies within and across jurisdictions, as well as with the insurance industry, to enable the sharing of lessons learned and access to broader expertise, in the aim of expediting the convergence of best practices.
Since June 2021, there have been several developments on the policy, technology, regulatory and scientific fronts, with implications for companies’ climate change risk assessment.
The evolving regulatory landscape for climate change risk assessment
Between June 2021 and May 2022, certain regulators launched new initiatives and published guidelines. A synthesis of these developments reveals the need for regulatory bodies to:
- Acknowledge the limitations of current tools, models and data for long-term quantitative scenario analysis (as evidence, the 2021 Bank of England Climate Biennial Exploratory Scenarios experiment concluded that projections of climate change losses are uncertain; the view that scenario analysis is still in its infancy, with notable data gaps; and the increasing recognition among some regulatory bodies that quantitative approaches can and should be complemented with qualitative assessments, especially over a longer time horizon);
- Stress the need to consider multiple scenarios representing different plausible pathways of transition or physical risks, and expand benchmark scenarios (typically NGFS) with sectoral and geographical granularity considerations;
- Recognise the principle of proportionality, with expectations linked to the size and organisational complexity of the company;
- Stress the importance of materiality in supervisory expectations for quantitative assessments as well as robust governance of climate change risks, with a need for transparency, particularly in relation to re/insurer investments in carbon-intensive sectors.
As of July 2022, there are still variations in the approaches used by regulators. Regulators agree, however, that this could impede comparisons across companies and jurisdictions as well as the ability to assess broader systemic economic and social impacts. Importantly, the International Association of Insurance Supervisors (IAIS) is working on promoting a globally consistent supervisory response to climate change, with a focus on three areas:
- standards,
- data
- and scenario analysis,
by providing guidance to regulatory bodies. The Financial Stability Board (FSB) is also issuing guidance on supervisory and regulatory approaches across borders and sectors to address market fragmentation and potential sources of systemic risk. Finally, the development of a global baseline for sustainability reporting standards with a focus on climate change, by the ISSB, aims to translate them further into harmonised inter-jurisdictional standards.

Strategic importance of aligning inside-out and outside-in climate risk assessment approaches
Companies are conducting two types of climate risk assessment:
- Inside-out analysis: This includes assessing the impact of the company’s actions on the climate by setting their climate targets (e.g. net zero targets) based on a variety of science-based approaches, such as those introduced by the UN Net-Zero Asset Owner Alliance (UN NZAOA) and the Science-Based Targets initiative (SBTi). For example, the UN-convened Net-Zero Alliances uses 1.5°C-compatible pathways, which may be far more ambitious than what companies and the real economy can deliver. In fact, the UN NZAOA has warned that the global economy does not move as is required by science, leading to a widening gap between companies’ climate targets and the real economy. Net-zero targets need to take this widening gap into account as this misalignment could lead to other financial and non-financial risks for the company, including reputation risk. This is further exacerbated by the fact that climate science is still evolving.
- Outside-in analysis: This involves assessing the resilience of the company’s business model to climate change risks, which is the focus of this report. It is important to emphasise that the development of the company’s strategy, transition plan and related actions cannot be done solely using inside-out analysis. Conducting outside-in analysis is critical, enabling the company to assess not only the impacts of climate change risks and their interactions, but also the implications of the possible range of activities under different scenarios on the firm’s business model. Of note, the inside-out view puts greater emphasis on ‘impact’ – which has a clear political component and should be grounded in materiality assumptions, which is the central objective of the outside-in analysis.
In summary, companies should seek to harmonise and align inside-out with outside-in climate change risk assessment efforts (Figure 1). In fact, a growing number of critics are calling out the misalignment of net-zero pledges by the financial sector, in light of their already committed investments in carbon-intensive sectors for the years to come. Critics are also raising the possibility of greenwashing, which could lead to potential climate litigation risk. Regarding the latter, some regulators are developing KPIs to assess and monitor the existence and level of greenwashing as part of their efforts to incorporate climate change factors into their regulatory mandate.